Counterfeiting costs the global economy over $500 billion annually. In pharmaceuticals alone, the WHO estimates that 10% of medicines worldwide are falsified. Luxury goods, electronics, automotive parts, and food products face similar threats.
QR codes — specifically serialized, GS1-compliant QR codes — offer a practical defense. Each product gets a unique identifier that can be verified by anyone with a smartphone. The technology doesn’t require special apps, proprietary hardware, or consumer education.
Here’s how it works and how to implement it.
Why Traditional Anti-Counterfeiting Fails
Most anti-counterfeiting methods rely on features that are difficult to replicate — holograms, special inks, watermarks, security threads. These have two fundamental problems:
-
Consumers can’t verify them. How do you know if a hologram is real? You’d need a reference image of the genuine hologram and enough expertise to spot differences. Most consumers simply can’t.
-
Counterfeiters improve. Holograms that were “impossible to copy” in 2015 are reproduced convincingly today. Physical security features are an arms race, and the counterfeiters are catching up.
Digital authentication through QR codes shifts the approach entirely. Instead of asking “does this physical feature look right?”, you ask “has this unique code been seen before, and where?”
Three Layers of QR-Based Authentication
Modern QR authentication uses three complementary layers. Each adds detection capability that the previous layers can’t provide.
Layer 1: Serial Verification Token (SVT)
Every product receives a unique serial number embedded in its QR code. When scanned, the code contacts a verification server that checks whether the serial number exists in the legitimate database.
How it works:
- During manufacturing, each product receives a unique serial number
- The serial is encoded in a GS1 Digital Link URL:
https://resolver.example.com/01/{GTIN}/21/{serial} - Consumer scans → server looks up serial → returns “authentic” or “unknown”
What it catches: codes with invented serial numbers that don’t exist in the manufacturer’s database.
Limitation: It doesn’t detect duplicated codes. If a counterfeiter copies a real code and applies it to fake products, SVT alone will verify each copy as “authentic.”
Layer 2: First-Scan Registration
The first time a code is scanned after manufacturing, it registers as “claimed.” Subsequent scans of the same code trigger a warning.
How it works:
- Product is manufactured → code is marked “unscanned” in the database
- First consumer scan → code status changes to “claimed,” scan location and time recorded
- Second scan of same code → alert: “This code was already verified on [date] in [location]”
What it catches: cloned codes. If a counterfeiter copies 10,000 QR codes from genuine products, the first 10,000 scans will register normally. But the genuine products will then trigger “already claimed” alerts when their buyers scan them.
Layer 3: Clone Detection Analytics
Statistical analysis of scan patterns identifies anomalies that suggest counterfeiting activity:
- Geographic impossible travel — The same serial number scanned in Tokyo and London within an hour
- Scan velocity spikes — A serial number scanned 50 times in one day (genuine products are scanned once or twice)
- Cluster analysis — Many serial numbers from the same batch scanned in a region where that batch was never shipped
These patterns generate alerts for investigation, even when individual scans appear legitimate.
For a technical deep dive into each layer, see our anti-counterfeiting technology page.
Implementation Steps
1. Set Up Serialization
Each product needs a globally unique identifier. If you’re already using GS1 standards (and you should be), this means adding AI 21 (serial number) to your GS1 Digital Link URL:
https://sprouter.gs/01/09506000134376/21/A7X9K2M4Serial numbers should be:
- Random — Sequential numbers are easy to predict and forge
- Sufficiently long — Minimum 8 alphanumeric characters for adequate entropy
- Non-reusable — Once assigned, a serial number is never recycled
2. Connect to a Verification Platform
Your resolver needs to:
- Store the mapping of serial numbers to product data
- Track scan events (time, location, device type)
- Return verification results to consumers
- Generate alerts for suspicious patterns
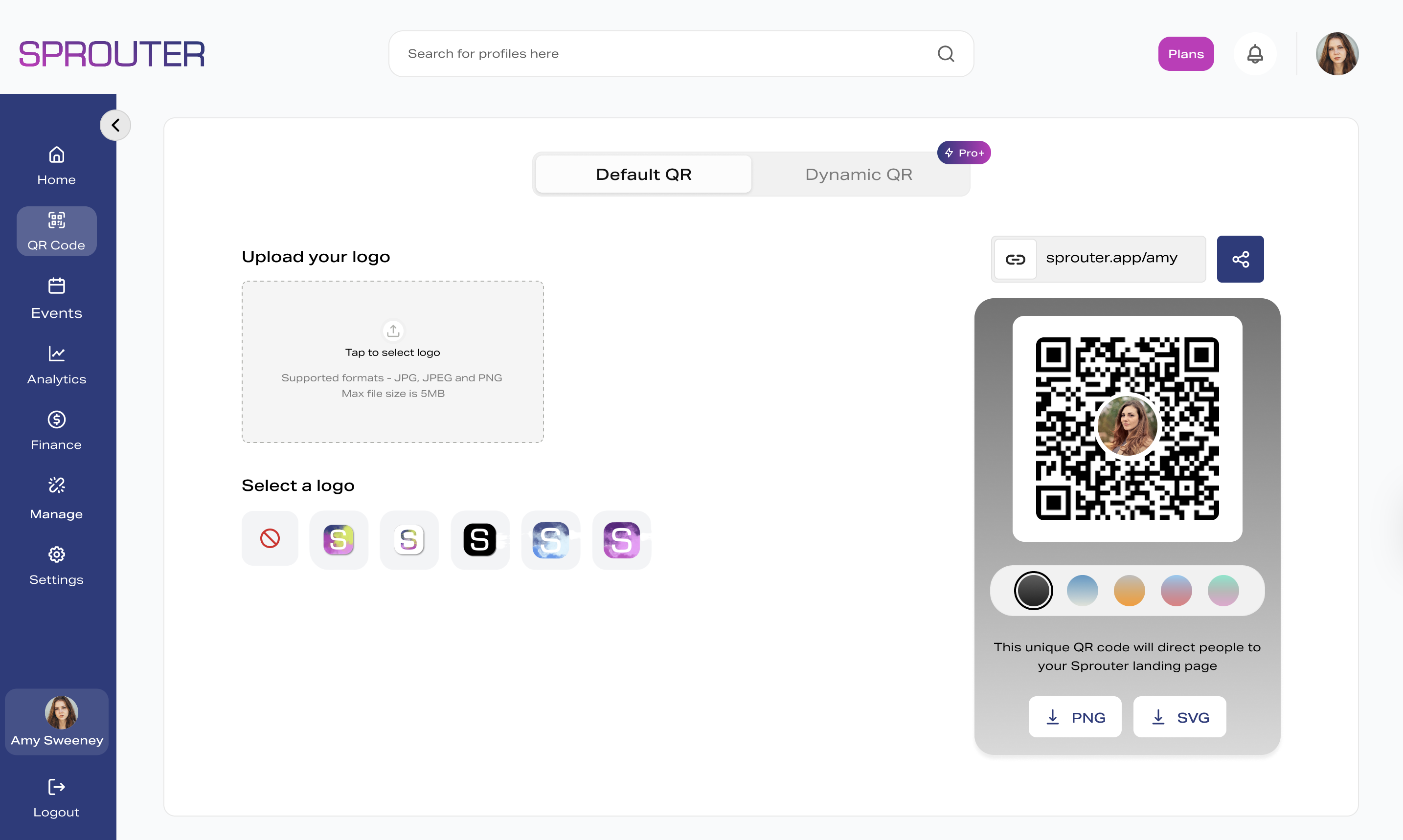
Sprouter’s GS1 platform includes authentication as part of the resolver infrastructure — no separate anti-counterfeiting vendor needed.
3. Design the Consumer Experience
When a consumer scans an authenticated product, they should see:
For verified products:
- Clear “Authentic” confirmation
- Product name, image, and details
- Manufacturing date and origin
- Optional: warranty registration, owner benefits
For suspicious products:
- Clear warning that the code has been previously verified
- Date and location of the first verification
- Instructions for reporting suspected counterfeits
- Link to the brand’s customer support
4. Monitor and Respond
Authentication is not “set and forget.” Active monitoring is required:
- Review clone detection alerts weekly
- Investigate geographic anomalies promptly
- Report confirmed counterfeits to authorities
- Update serial databases as new products ship
Industries Where This Matters Most
Pharmaceuticals
The WHO estimates that 10% of medicines in low- and middle-income countries are substandard or falsified. Serialized QR codes enable track-and-trace from manufacturer to patient. The EU Falsified Medicines Directive already requires serialization — GS1 Digital Link provides the standard.
Luxury Goods
A handbag, watch, or pair of sneakers worth thousands of dollars needs provable authenticity. QR authentication provides a digital certificate of authenticity that travels with the product through resale.
Electronics and Auto Parts
Counterfeit electronic components cause approximately $75 billion in damages annually. QR verification confirms genuine parts from authorized manufacturers.
Wine and Spirits
Fake premium wines and spirits are a growing problem. A serialized QR code on the bottle lets consumers verify authenticity before opening — and lets distributors verify stock integrity.
What About Tampering?
A valid concern: what stops someone from covering a genuine QR code with a counterfeit one?
Tamper-evident labels. Print the QR code on a label that visibly destructs when peeled. The code becomes unscannable after removal, so it can’t be transferred to a counterfeit product.
Substrate integration. Print the QR directly on the packaging (not on a label). This makes replacement significantly harder — you’d have to replace the entire package.
Digital verification layers. Combine QR authentication with other digital signals. If the QR code claims to be product X but NFC data (if present) says product Y, that’s a red flag.
No system is tamper-proof. The goal is to make counterfeiting more expensive and detectable, not to achieve perfection.
Getting Started with Sprouter
Sprouter’s GS1 platform includes product authentication as part of the integrated resolver:
- Serial number management — Generate, assign, and track unique serial numbers
- Three-layer verification — SVT, first-scan registration, and clone detection analytics
- Brand protection dashboard — Real-time monitoring of scan patterns and alerts
- Consumer-facing verification — Branded authentication pages your customers see when they scan
Start with a pilot on your highest-value or most-counterfeited product line. Sprouter’s enterprise solutions team can help design the rollout.